By Robert McMillan
The Federal Bureau of Investigation moved to dismantle a large
network of hacked routers and storage devices that Cisco Systems
Inc. and U.S. and Ukraine authorities said could be used to launch
a massive cyberattack or knock hundreds of thousands of internet
users offline.
The FBI said late Wednesday that it has seized control of the
internet domain that was used by the computer network's "command
and control" server to issue instructions to infected devices. The
agency said it has begun an effort to clean up the estimated
half-million infected devices.
That effort will take some time, security researchers say.
Researchers and Ukranian authorities warned earlier that the
network could be used to launch an attack timed to the final match
in soccer's UEFA Champions League competition taking place Saturday
in Kiev.
The hacked devices, which span 54 countries, are infected with
sophisticated software called VPNFilter that can install other
software or even internal changes that render the devices unusable,
according to Craig Williams, a security researcher with Cisco.
The network had grown quietly since 2016 but expanded rapidly
within Ukraine around May 8, with systems in the country now making
up about half of the infected machines on the network, Mr. Williams
said Wednesday before the FBI's announcement.
"They're clearly targeting Ukraine," he said. "The fact that we
saw this being spun up so quickly is evidence that something is
being planned."
Ukrainian authorities, in an earlier statement, said they
believed this could be a precursor to a cyberattack by Russia
targeted to the Champions League final.
A representative from the Ukrainian Embassy in Washington, D.C.,
didn't respond to requests for further comment.
Ukraine has blamed Russia for a wave of disruptive cyberattacks
that have shut down electricity and hacked computers across the
country over the past three years. Ukraine was the main target of
last year's Petya computer virus, cybersecurity researchers
believe, an attack launched shortly before a national holiday
celebrating the adoption of Ukraine's constitution.
Earlier this year, authorities in the U.S. and U.K. blamed
Russia for the Petya outbreak. Russia has called the accusations
"baseless."
The FBI said that the network of hacked computers was created by
a group known as APT 28, or Fancy Bear, which has also been linked
to the 2016 hacking of the Democratic National Committee. U.S.
authorities said last year that APT 28 is made up of hackers
working for the Russian intelligence service.
It is unclear what comes next, researchers and authorities say.
But VPNFilter has the capabilities to install software that can
steal sensitive information from the network such as passwords or
even data on power plants or factory-floor computers, Mr. Williams
said.
The FBI's takedown will prevent recently infected or rebooted
devices from receiving instructions from the command-and-control
server, but the many routers and storage devices that had already
downloaded these instructions before the FBI's takedown remain
under the control of the hackers until they are restarted, said
Vikram Thakur a technical director with security vendor
Symantec.
Whoever built the network could launch a new virus like Petya,
attack power plants or disrupt computer systems connected to the
coming Champions League game, Mr. Williams said. After a
cyberattack, the creators could cover their steps by wiping out the
infected device's software, effectively leaving hundreds of
thousands of people without internet access, he said.
"The reality is, this attacker has limitless options," Mr.
Williams said.
According to Cisco, the VPNFilter malware affects certain
Linksys routers built by Belkin International Inc. as well as some
built by Netgear Inc., SIA Mikrot kls (MikroTik), and TP-Link
Technologies Co. and some storage devices built by QNAP Systems,
Inc.
Many of these devices can be taken over using known well-known
attacks or default administrative passwords, Mr. Williams said.
Netgear and TP-Link published security advisories Wednesday
saying the companies are investigating the VPNFilter malware. They
advised users to update their routers' software and to avoid using
the default passwords.
The other device makers didn't immediately respond to requests
for comment.
The U.S. Department of Homeland Security on Wednesday issued a
warning about VPNFilter, saying that the software "has the
potential to cut off internet access for hundreds of thousands of
users."
After years of focusing on personal computers, hackers have
increasingly turned to the so-called Internet of Things -- routers,
storage devices, video recorders and other internet-connected
devices -- that don't typically run antivirus software and are can
often be accessed using default usernames and passwords.
In 2016, a network of about 300,000 such infected devices caused
a widespread internet outage in the U.S. by launching a massive
online attack against an internet service provider.
Write to Robert McMillan at Robert.Mcmillan@wsj.com
(END) Dow Jones Newswires
May 23, 2018 22:26 ET (02:26 GMT)
Copyright (c) 2018 Dow Jones & Company, Inc.
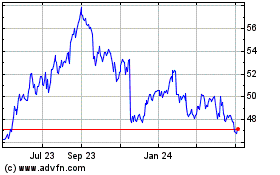
Cisco Systems (NASDAQ:CSCO)
Historical Stock Chart
From Mar 2024 to Apr 2024
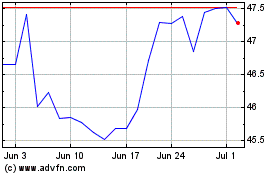
Cisco Systems (NASDAQ:CSCO)
Historical Stock Chart
From Apr 2023 to Apr 2024