Stolen Credentials Selling on the Dark Web for Price of a Gallon of Gas
July 21 2022 - 12:30PM

HP Inc. (NYSE: HPQ) today released
The Evolution of
Cybercrime: Why the Dark Web is Supercharging the Threat Landscape
and How to Fight Back – an HP Wolf Security Report. The
findings show cybercrime is being supercharged through “plug and
play” malware kits that make it easier than ever to launch attacks.
Cyber syndicates are collaborating with amateur attackers to target
businesses, putting our online world at risk.
The HP Wolf Security threat team worked with Forensic Pathways,
a leading group of global forensic professionals, on a three-month
dark web investigation, scraping and analyzing over 35 million
cybercriminal marketplaces and forum posts to understand how
cybercriminals operate, gain trust, and build reputation.
Key findings include:
- Malware is cheap and readily
available – Over three quarters (76%) of malware
advertisements listed, and 91% of exploits (i.e. code that gives
attackers control over systems by taking advantage of software
bugs), retail for under $10 USD. The average cost of compromised
Remote Desktop Protocol credentials is just $5 USD. Vendors are
selling products in bundles, with plug-and-play malware kits,
malware-as-a-service, tutorials, and mentoring services reducing
the need for technical skills and experience to conduct complex,
targeted attacks – in fact, just 2-3% of threat actors today are
advanced coders1.
- The irony of ‘honor amongst
cyber-thieves’ – Much like the legitimate online retail
world, trust and reputation are ironically essential parts of
cybercriminal commerce: 77% of cybercriminal marketplaces analyzed
require a vendor bond – a license to sell – which can cost up to
$3,000. 85% of these use escrow payments, and 92% have a
third-party dispute resolution service. Every marketplace provides
vendor feedback scores. Cybercriminals also try to stay a step
ahead of law enforcement by transferring reputation between
websites – as the average lifespan of a dark net Tor website is
only 55 days.
- Popular software is giving
cybercriminals a foot in the door – Cybercriminals are
focusing on finding gaps in software that will allow them to get a
foothold and take control of systems by targeting known bugs and
vulnerabilities in popular software. Examples include the Windows
operating system, Microsoft Office, web content management systems,
and web and mail servers. Kits that exploit vulnerabilities in
niche systems command the highest prices (typically ranging from
$1,000-$4,000 USD). Zero Days (vulnerabilities that are not yet
publicly known) are retailing at 10s of thousands of dollars on
dark web markets.
“Unfortunately, it’s never been easier to be a cybercriminal.
Complex attacks previously required serious skills, knowledge and
resource. Now the technology and training is available for the
price of a gallons of gas. And whether it’s having your company ad
customer data exposed, deliveries delayed or even a hospital
appointment cancelled, the explosion in cybercrime affects us all,”
comments report author Alex Holland, Senior Malware Analyst at HP
Inc.
“At the heart of this is ransomware, which has created a new
cybercriminal ecosystem rewarding smaller players with a slice of
the profits. This is creating a cybercrime factory line, churning
out attacks that can be very hard to defend against and putting the
businesses we all rely on in the crosshairs,” Holland adds.
HP consulted with a panel of experts from cybersecurity and
academia – including ex-black hat hacker Michael ‘Mafia Boy’ Calce
and authored criminologist, Dr. Mike McGuire – to understand how
cybercrime has evolved and what businesses can do to better protect
themselves against the threats of today and tomorrow. They warned
that businesses should prepare for destructive data denial attacks,
increasingly targeted cyber campaigns, and cybercriminals using
emerging technologies like artificial intelligence to challenge
organizations’ data integrity.
To protect against current and future threats, the report offers
up the following advice for businesses:
Master the basics to reduce cybercriminals’
chances: Follow best practices, such as multi-factor
authentication and patch management; reduce your attack surface
from top attack vectors like email, web browsing and file
downloads; and prioritize self-healing hardware to boost
resilience.
Focus on winning the game: plan for the worst;
limit risk posed by your people and partners by putting processes
in place to vet supplier security and educate workforces on social
engineering; and be process-oriented and rehearse responses to
attacks so you can identify problems, make improvements and be
better prepared.
Cybercrime is a team sport. Cybersecurity must be
too: talk to your peers to share threat information and
intelligence in real-time; use threat intelligence and be proactive
in horizon scanning by monitoring open discussions on underground
forums; and work with third-party security services to uncover weak
spots and critical risks that need addressing.
“We all need to do more to fight the growing cybercrime
machine,” says Dr. Ian Pratt, Global Head of Security for Personal
Systems at HP Inc. “For individuals, this means becoming cyber
aware. Most attacks start with a click of a mouse, so thinking
before you click is always important. But giving yourself a safety
net by buying technology that can mitigate and recover from the
impact of bad clicks is even better.”
“For businesses, it’s important to build resiliency and shut off
as many common attack routes as possible,” Pratt continues. “For
example, cybercriminals study patches on release to reverse
engineer the vulnerability being patched and can rapidly create
exploits to use before organizations have patched. So, speeding up
patch management is important. Many of the most common categories
of threat such as those delivered via email and the web can be
fully neutralized through techniques such as threat containment and
isolation, greatly reducing an organization’s attack surface
regardless of whether the vulnerabilities are patched or not.”
You can read the full report here
https://threatresearch.ext.hp.com/evolution-of-cybercrime-report/
Media contacts:Vanessa Godsal / vgodsal@hp.com
About the research
The Evolution of Cybercrime – The Evolution of Cybercrime: Why
the Dark Web is Supercharging the Threat Landscape and How to Fight
Back – an HP Wolf Security Report is based on findings from:
- An independent study carried out by
dark web investigation firm Forensic Pathways and commissioned by
HP Wolf Security. The firm collected dark web marketplace listings
using their automated crawlers that monitor content on the Tor
network. Their Dark Search Engine tool has an index consisting of
>35 million URLs of scraped data. The collected data was
examined and validated by Forensic Pathway’s analysts. This report
analyzed approximately 33,000 active websites across the dark web,
including 5,502 forums and 6,529 marketplaces. Between February and
April 2022, Forensic Pathways identified 17 recently active
cybercrime marketplaces across the Tor network and 16 hacking
forums across the Tor network and the web containing relevant
listings that comprise the data set.
- The report also includes threat
telemetry from HP Wolf Security and research into the leaked
communications of the Conti ransomware group.
- Interviews with and contributions
from a panel of cybersecurity experts including:
- Alex Holland, report author, Senior
Malware Analyst at HP Inc.
- Joanna Burkey, Chief Information
Security Officer at HP Inc.
- Dr. Ian Pratt, Global Head of
Security for Personal Systems at HP Inc.
- Boris Balacheff, Chief Technologist
for Security Research and Innovation at HP Labs, HP Inc.
- Patrick Schlapfer, Malware Analyst
at HP Inc.
- Michael Calce, former black hat
“MafiaBoy”, HP Security Advisory Board Chairman, CEO of
decentraweb, and President of Optimal Secure.
- Dr. Mike McGuire, senior lecturer of
criminology at the University of Surrey, UK and authored expert on
cybersecurity.
- Robert Masse, HP Security Advisory
Board member and Partner at Deloitte.
- Justine Bone, HP Security Advisory
Board member and CEO at Medsec.
About HP
HP Inc. is a technology company that believes one thoughtful
idea has the power to change the world. Its product and service
portfolio of personal systems, printers, and 3D printing solutions
helps bring these ideas to life. Visit http://www.hp.com.
About HP Wolf Security
From the maker of the world’s most secure PCs2 and Printers3, HP
Wolf Security is a new breed of endpoint security. HP’s portfolio
of hardware-enforced security and endpoint-focused security
services are designed to help organizations safeguard PCs,
printers, and people from circling cyber predators. HP Wolf
Security provides comprehensive endpoint protection and resiliency
that starts at the hardware level and extends across software and
services.
©Copyright 2022 HP Development Company, L.P. The information
contained herein is subject to change without notice. The only
warranties for HP products and services are set forth in the
express warranty statements accompanying such products and
services. Nothing herein should be construed as constituting an
additional warranty. HP shall not be liable for technical or
editorial errors or omissions contained herein.
1 According to Michael Calce, former black hat “MafiaBoy”, HP
Security Advisory Board Member, CEO of decentraweb, and President
of Optimal Secure2 Based on HP’s unique and comprehensive security
capabilities at no additional cost among vendors on HP Elite PCs
with Windows and 8th Gen and higher Intel® processors or AMD Ryzen™
4000 processors and higher; HP ProDesk 600 G6 with Intel® 10th Gen
and higher processors; and HP ProBook 600 with AMD Ryzen™ 4000 or
Intel® 11th Gen processors and higher.3 HP’s most advanced embedded
security features are available on HP Enterprise and HP Managed
devices with HP FutureSmart firmware 4.5 or above. Claim based on
HP review of 2021 published features of competitive in-class
printers. Only HP offers a combination of security features to
automatically detect, stop, and recover from attacks with a
self-healing reboot, in alignment with NIST SP 800-193 guidelines
for device cyber resiliency. For a list of compatible products,
visit: hp.com/go/PrintersThatProtect. For more information, visit:
hp.com/go/PrinterSecurityClaims.
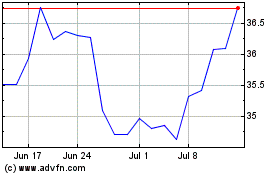
HP (NYSE:HPQ)
Historical Stock Chart
From Aug 2024 to Sep 2024
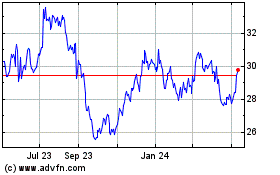
HP (NYSE:HPQ)
Historical Stock Chart
From Sep 2023 to Sep 2024