McAfee Labs Report Reviews Five Years of Hardware and Software Threat Evolution
September 01 2015 - 12:01AM
Business Wire
Report Provides Five-Year Threat
Retrospective, GPU Malware Assessment, and Techniques for
Exfiltrating Data from Corporate Networks; Ransomware Rises 127%
from Q2 2014 to Q2 2015
Intel® Security today released its McAfee Labs Threats
Report: August 2015, which includes a critique of graphics
processing unit (GPU) malware claims, an investigation of the top
cybercriminal exfiltration techniques, and a five-year
retrospective on the evolution of the threat landscape since Intel
Corporation’s announcement of the McAfee acquisition.
McAfee Labs commemorates the five-year anniversary of the
Intel-McAfee union by comparing what researchers thought would
happen beginning in 2010 with what actually happened in the realm
of hardware and software security threats. Key researchers and
executives reviewed our predictions on the security capabilities of
silicon, the challenges of emerging hard-to-detect attacks, and our
2010 expectations for new device types versus the reality of the
marketplace.
The five-year threat landscape analysis suggests:
- Intel Security foresaw threats
targeting hardware and firmware components and threatening runtime
integrity
- Increasingly evasive malware and
long-running attacks did not surprise us but some of the specific
tactics and techniques were unimagined five years ago
- Although the volume of mobile devices
has increased even faster than we expected, serious broad-based
attacks on those devices has grown much more slowly than we
thought
- We are seeing just the beginnings of
attacks and breaches against IoT devices
- Cloud adoption has changed the nature
of some attacks, as devices are attacked not for the small amount
of data that they store, but as a path to where the important data
resides
- Cybercrime has grown into a
full-fledged industry with suppliers, markets, service providers,
financing, trading systems and a proliferation of business
models
- Businesses and consumers still do not
pay sufficient attention to updates, patches, password security,
security alerts, default configurations, and other easy but
critical ways to secure cyber and physical assets
- The discovery and exploitation of core
Internet vulnerabilities has demonstrated how some foundational
technologies are underfunded and understaffed
- There is growing, positive
collaboration between the security industry, academia, law
enforcement and governments to take down cybercriminal
operations
“We were impressed by the degree to which three key factors –
expanding attack surfaces, the industrialization of hacking, and
the complexity and fragmentation of the IT security market –
accelerated the evolution of threats, and size and frequency of
attacks,” said Vincent Weafer, senior vice president, Intel
Security’s McAfee Labs. “To keep pace with such momentum, the
cybersecurity community must continue to improve threat
intelligence sharing, recruit more security professionals,
accelerate security technology innovation, and continue to engage
governments so they can fulfill their role to protect citizens in
cyberspace.”
The August report also probes into the details of three
proofs-of-concept (PoC) for malware exploiting GPUs in attacks.
While nearly all of today’s malware is designed to run from main
system memory on the central processing unit (CPU), these PoCs
leverage the efficiencies of these specialized hardware components
designed to accelerate the creation of images for output to a
display. The scenarios suggest hackers will attempt to leverage
GPUs for their raw processing power, using them to evade
traditional malware defenses by running code and storing data where
traditional defenses do not normally watch for malicious code.
Reviewing the PoCs, Intel Security agrees that moving portions
of malicious code off of the CPU and host memory reduces the
detection surface for host-based defenses. However, researchers
argue that, at a minimum, trace elements of malicious activity
remain in memory or CPUs, allowing endpoint security products to
detect and remediate threats.
McAfee Labs also details techniques cybercriminals use to
exfiltrate a wide variety of information on individuals from
corporate networks: names, dates of birth, addresses, phone
numbers, social security numbers, credit and debit card numbers,
health care information, account credentials, and even sexual
preferences. In addition to tactics and techniques used by
attackers, this analysis examines attacker types, their
motivations, and their likely targets, as well as the policies
businesses should embrace to better detect exfiltration.
The August 2015 report also identified a number of other
developments in the second quarter of 2015:
- Ransomware. Ransomware continues
to grow very rapidly – with the number of new ransomware samples
rising 58% in Q2. The total number of ransomware samples grew 127%
from Q2 2014 to Q2 2015. We attribute the increase to fast-growing
new families such as CTB-Locker, CryptoWall, and others.
- Mobile slump. The total number
of mobile malware samples grew 17% in Q2. But mobile malware
infection rates declined about 1% per region this quarter, with the
exception of North America, which dropped almost 4%, and Africa,
which was unchanged.
- Spam botnets. The trend of
decreasing botnet-generated spam volume continued through Q2, as
the Kelihos botnet remained inactive. Slenfbot again claims the top
rank, followed closely by Gamut, with Cutwail rounding out the top
three.
- Suspect URLs. Every hour in Q2
more than 6.7 million attempts were made to entice McAfee customers
into connecting to risky URLs via emails, browser searches,
etc.
- Infected files. Every hour in Q2
more than 19.2 million infected files were exposed to McAfee
customers’ networks.
- PUPs up. Every hour in Q2 an
additional 7 million potentially unwanted programs (PUPs) attempted
installation or launch on McAfee-protected networks.
For more information, please read the full report: McAfee Labs
Threats Report: August 2015.
For guidance on how organizations can better protect their
enterprise from the threats detailed in this quarter’s report,
please visit: Enterprise Blog.
About McAfee Labs
McAfee Labs is the threat research division of Intel Security
and one of the world’s leading sources for threat research, threat
intelligence, and cybersecurity thought leadership. The McAfee Labs
team of more than 400 researchers collects threat data from
millions of sensors across key threat vectors—file, web, message,
and network. It then performs cross-vector threat correlation
analysis and delivers real-time threat intelligence to tightly
integrated McAfee endpoint, content, and network security products
through its cloud-based McAfee Global Threat Intelligence service.
McAfee Labs also develops core threat detection technologies—such
as application profiling, and graylist management—that are
incorporated into the broadest security product portfolio in the
industry.
About Intel Security
McAfee Labs is now part of Intel Security. With its Security
Connected strategy, innovative approach to hardware-enhanced
security, and unique McAfee Global Threat Intelligence, Intel
Security is intensely focused on developing proactive, proven
security solutions and services that protect systems, networks, and
mobile devices for business and personal use around the world.
Intel Security is combining the experience and expertise of McAfee
with the innovation and proven performance of Intel to make
security an essential ingredient in every architecture and on every
computing platform. The mission of Intel Security is to give
everyone the confidence to live and work safely and securely in the
digital world. www.intelsecurity.com.
No computer system can be absolutely secure.
Note: Intel and the Intel and McAfee logos, are trademarks of
Intel Corporation or McAfee, Inc. in the US and/or other
countries.
*Other names and brands may be claimed as the property of
others.
View source
version on businesswire.com: http://www.businesswire.com/news/home/20150831005241/en/
Intel SecurityChris Palm, 408-346-3089chris.palm@intel.comorZeno
GroupJanelle Dickerson,
650-801-0936Janelle.Dickerson@zenogroup.com
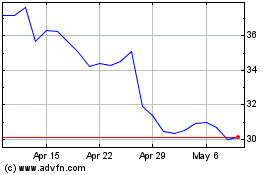
Intel (NASDAQ:INTC)
Historical Stock Chart
From Aug 2024 to Sep 2024
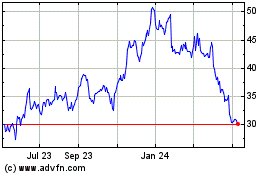
Intel (NASDAQ:INTC)
Historical Stock Chart
From Sep 2023 to Sep 2024