By Nick Kostov, Jenny Gross and Stu Woo
The cyberattack that spread around the globe over the weekend,
hitting businesses, hospitals and government agencies in at least
150 countries, is likely to keep growing as people around the world
return to work, law-enforcement authorities warned.
Investigators launched a far-reaching hunt for the perpetrator,
as institutions around the world worked to mitigate damage from the
highest-profile computer-worm outbreak in nearly a decade. Europe's
police-coordination agency estimated at least 200,000 individual
terminals had fallen victim to the attack, while Chinese
authorities put the number as high as 1 million world-wide.
"This is something we haven't seen before," Europol director Rob
Wainwright told U.K. television channel ITV. "The global reach is
unprecedented."
Among the highest-profile corporate victims was French auto
maker Renault SA, which was forced to shut down factories across
Europe.
When workers arrived at a Renault plant in Sandouville, in
northern France, on Saturday morning, TV screens that usually
update staff on company productivity had a different message: A
demand, in French, for $300 in ransom. The screens also showed two
clocks counting down the time Renault had to deliver the payments
before the factory's files were deleted.
"Everyone was running around, saying we've been hacked," said
Mohamed Amri, a 41-year-old parts maker. "It spread like
wildfire."
The cyberattack involved a ransomware dubbed WannaCry, designed
to spread quickly after infecting computers. Files on affected
computers were encrypted, and users were told to pay a ransom with
bitcoin, an untraceable online currency, to unscramble them.
So far, the virus hasn't been blamed for destroying hardware
itself. Where users have backed up data, long-term damage likely
can be limited. But some targets responding to the attack had to
shut down entire systems to help combat or slow the virus.
The computers of dozens of hospitals and health-care facilities
in the U.K. were affected, but officials said that -- so far --
there was no indication patients had been put in grave danger from
the outages. They also said patient data hadn't been stolen. German
train operator Deutsche Bahn AG said its trains were running as
usual despite the attack, though it was straining to get its
computer systems back online. U.S. delivery company FedEx Corp. was
also affected.
The police force in Yancheng, a Chinese city 200 miles north of
Shanghai, apologized on its official social-media account for being
unable to provide certain services because of the virus. A swath of
Chinese gasoline stations, run by China National Petroleum Corp.,
was closed because of the attack.
Russia's central bank said domestic banks had been targeted,
according to state news agency RIA. Sberbank, Russia's largest
lender, said Friday night its cyber infrastructure had been
targeted but that it had fended off the attack, news wires
reported. The country's interior ministry said around 1,000
computers had been affected, but that the attack had been
localized.
Britain's National Cyber Security Center, a government agency,
said Sunday that there hadn't been any new attacks similar to
Friday's, but that existing infections from the malware could
continue to spread within networks.
"This means that as a new working week begins it is likely, in
the U.K. and elsewhere, that further cases of ransomware may come
to light, possibly at a significant scale," the agency said.
The virus was slowed down over the weekend by the identification
and activation of a "kill switch" embedded in the virus' code,
computer experts said. But few believe it was halted completely,
and one security expert had identified late Sunday at least one new
strain, unaffected by the kill switch, though it was spreading
slowly.
While the U.S. appears relatively unscathed compared with Europe
and Asia, the Federal Bureau of Investigation, the National
Security Agency and the Department of Homeland Security all were on
the case. Tom Bossert, President Donald Trump's homeland security
and counterterrorism adviser, held emergency meetings with cabinet
members Friday night and Saturday morning at the White House, an
administration official said Sunday.
Government agencies have started a global manhunt for the
perpetrator -- a complex international probe that requires the same
sort of cooperation and intelligence sharing common in large
terrorist attacks.
Security experts have been able to track a small amount of
bitcoin transactions they said were likely ransom linked to the
attack. It was impossible to say how many companies were paying, or
whom they were paying. Unlike bank and other financial accounts,
bitcoin accounts are theoretically untraceable to their owners.
The attack took advantage of security vulnerabilities in
Microsoft Corp. software that was either too old to be supported by
security patches or hadn't been patched by users. Microsoft on
Sunday said that the software tool used in the attack came from
code stolen from the National Security Agency. The NSA has declined
to comment on the matter.
None of the infected computers had installed a March 14 software
patch by Microsoft that stopped the worm, either because they were
running older versions of Microsoft Windows that no longer received
software updates, or because companies had simply delayed
installing the software.
An early sign of trouble at the Renault plant in Sandouville
came when the assembly line's alarm system stopped working early
Saturday -- right after the demand for ransom appeared on TV
screens. Tanguy Deschamps, a 38-year-old who was working at the
factory when the virus hit, said the alarms were failing to sound
whenever workers tried to alert others to crooked or improperly
welded parts.
Management told workers to unplug the machines.
At 1 a.m. French time, Malik Denon was making final alterations
on cars that were almost finished when his boss came down to tell
him Renault had been hacked. At first, Mr. Denon thought it was a
joke, but his boss wasn't laughing.
"He was panicked," Mr. Denon said.
Séverin Beuche, a local IT expert, was called to the plant
Saturday morning to help restart the site.
"I've never seen something of this size," Mr. Beuche said. He
and a crisis unit worked around the clock to rebuild servers that
had been crippled.
The auto maker's cybersecurity team time pored over company
computer systems before the factories were due to resume full
production on Monday.
The assembly remained dormant Saturday. Instead of making car
parts, workers were asked to tidy up the factory. Union officials
estimated that 100 cars weren't produced at the plant as a result
of the hack.
--Robert McMillan in San Francisco, Liza Lin in Shanghai and
Louise Radnofsky in Washington contributed to this article.
Write to Nick Kostov at Nick.Kostov@wsj.com, Jenny Gross at
jenny.gross@wsj.com and Stu Woo at Stu.Woo@wsj.com
(END) Dow Jones Newswires
May 14, 2017 19:19 ET (23:19 GMT)
Copyright (c) 2017 Dow Jones & Company, Inc.
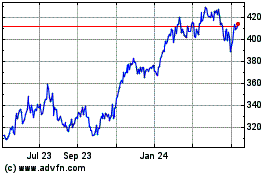
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From Aug 2024 to Sep 2024
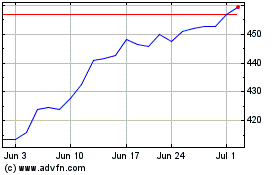
Microsoft (NASDAQ:MSFT)
Historical Stock Chart
From Sep 2023 to Sep 2024