-- Optiv to Share Significant Expertise to Help
Organizations More Successfully Address Identity at the Project,
Problem and Strategy Levels --
Optiv Security, a market-leading provider of end-to-end cyber
security solutions, today announced that its security experts will
participate in eight different sessions at the 2016 Cloud Identity
Summit (CIS). The speakers will share insights based on their
expertise in helping organizations plan, build and run successful
cloud and identity-focused security programs. The summit is
scheduled to take place June 6-9, 2016 at the New Orleans Marriott
in Louisiana.
Sessions include:
Identity Really is the New
PerimeterWho/Topic: With the proliferation of advanced
threats, juxtaposed against increased connectivity demands of
employees, vendors, business partners and consumers; identity is
being looked at more than ever as a layer of defense, and in many
ways, as the new perimeter. In this session, Aubrey Turner, client
solutions director, will discuss how various types of technology
are adapting to embrace this paradigm, and high-level approaches to
prepare and react to this evolving security
model.When/Where: Monday, June 6 from 4:15 – 4:40 p.m.
CST/Salon E
Identity. It's Not Just a Thing, It's
Integrated into EverythingWho/Topic: Many organizations
have made investments in identity and access management (IAM) to
support functions like user lifecycle management, identity
governance or single sign-on. The identity industry is evolving,
and identity is becoming the critical core of any security
strategy. Attendees of this session led by Robert Block, vice
president, strategic solutions, will learn how expanding the role
of identity in their environment can revolutionize their approach
to cyber security.When/Where: Tuesday, June 7 from 9:30 –
9:55 a.m. CST/Salon E
CISO & Identity = (Oil & Water) or
(Oil & Vinegar) and What that Means to Your
OrganizationWho/Topic: Too many CISOs do not embrace
identity and its importance to a successful cyber security program,
making the CISO and identity seem like oil and vinegar. During this
session, Larry Whiteside Jr., vice president, executive strategy,
healthcare and critical infrastructure solutions, will explain how
oil and vinegar are not just great on salads, but also vital for
the success of a CISO’s cyber security strategy.When/Where:
Tuesday, June 7 from 10:40 – 11:05 a.m. CST/Salon E
“Optivized” Cloud Security – Establishing
the Pillars for a Successful CloudSec ProgramWho/Topic:
The adoption of cloud computing is a clear reaction to enterprises’
need for agility, elasticity and cost-effective IT solutions. In
mature organizations, security professionals are in a rare position
to address security early on in adoption cycles or even propose
more secure alternatives that enable the adoption of innovative IT
delivery. JD Sherry, vice president, strategy and innovation, will
inform attendees about the common pillars one should include in
their cloud security strategy.When/Where: Tuesday, June 7
from 2:30 – 2:55 p.m. CST/Salon E
Panel: Federated Identity for Large Scale
DeploymentsWho/Topic: With the rise of cloud-based
business and customer portals, enterprises need to be prepared to
serve an exploding number of constituents, while also providing
single sign-on and seamless UX for all users. In this session, Joe
Greene, director, information security, and a panel of experts will
lay out some key advantages of identity virtualization through the
lens of federation and discuss the enhanced infrastructure speed,
flexibility and security their respective IAM teams were able to
achieve.When/Where: Wednesday, June 8 from 10:55 – 11:20
a.m. CST/Studio 1/2
Keynote Panel: Identity Defined Security –
Enabling the R/evolutionWho/Topic: The traditional IT
security approach of putting trusted users, devices and
applications behind a single perimeter is no longer sufficient. In
our increasingly decentralized, deperimeterized,
'bring-your-own-anything' world, we need a better approach to
protect users, customers, data and assets. In this panel featuring
Robert Block, leaders from the Identity Defined Security Alliance
will discuss this new approach to security and how it can help
deliver a better and safer experience.When/Where: Wednesday,
June 8 from 5:30 – 6:00 p.m. CST/Grand Ballroom
Secure DevOps – Shared
ResponsibilityWho/Topic: Infrastructure as a Service
(IaaS) assets are completely under your control and require you to
perform all of the necessary security configuration and management
tasks. Today’s IT and security organizations see the world of IaaS
through a variety of lenses depending on the charter the business
has given them to transform how they deliver IT services. In this
session, JD Sherry will walk attendees through some of the
thoughtful considerations about how to secure these services and
not slow down the speed of adoption of cloud
infrastructure.When/Where: Thursday, June 9 from 9:30 – 9:55
a.m. CST/Salon E
Cloud Security Program, Best in
Breed?Who/Topic: More and more organizations are in the
process of planning, building or running a cloud security program.
Whether identifying, encrypting, protecting or securing data in
today's enterprises, Tim Benner, senior client solutions architect,
will help session attendees craft an effective plan using the
best-in-breed technology.When/Where: Thursday, June 9 from
10:40 – 11:05 a.m. CST/Salon E
Optiv recently expanded its leadership position in IAM with its
acquisition of IAM solutions and services provider Advancive. The
transaction helped Optiv create the industry’s deepest and broadest
bench of IAM experts with experience in and capabilities across an
extensive technology portfolio. The move also gave Optiv additional
expertise to develop new and innovative IAM services and solutions
to better help clients plan, build and run holistic IAM security
programs that meet their specific business needs.
Optiv is proud to be a founding security sponsor of the CIS and
will exhibit at booth number one. Media wishing to interview
Optiv’s experts should contact Jennifer Torode at
jtorode@chenpr.com or (781) 672-3119.
About Optiv SecurityOptiv is a market-leading provider of
end-to-end cyber security solutions. We help clients plan, build
and run successful cyber security programs that achieve business
objectives through our depth and breadth of cyber security
offerings, extensive capabilities and proven expertise in cyber
security strategy, managed security services, incident response,
risk and compliance, security consulting, training and support,
integration and architecture services, and security technology. A
Blackstone (NYSE: BX) portfolio company, Optiv maintains premium
partnerships with more than 300 of the leading security technology
manufacturers. For more information, visit www.optiv.com or follow
us at www.twitter.com/optiv, www.facebook.com/optivinc and
www.linkedin.com/company/optiv-inc.
View source
version on businesswire.com: http://www.businesswire.com/news/home/20160606005967/en/
For Optiv SecuritySusan Vaillancourt,
603-459-8906susan.vaillancourt@optiv.comorJennifer Torode,
781-672-3119jtorode@chenpr.com
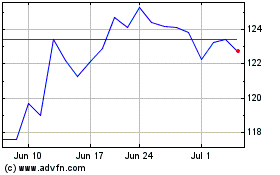
Blackstone (NYSE:BX)
Historical Stock Chart
From Aug 2024 to Sep 2024
Blackstone (NYSE:BX)
Historical Stock Chart
From Sep 2023 to Sep 2024
