Iranian hackers infiltrated the control system of a small dam
less than 20 miles from New York City two years ago, sparking
concerns that reached to the White House, according to former and
current U.S. officials and experts familiar with the previously
undisclosed incident.
The breach came amid attacks by hackers linked to Iran's
government against the websites of U.S. banks, and just a few years
after American spies had damaged an Iranian nuclear facility with a
sophisticated computer worm called Stuxnet. In October 2012,
then-Defense Secretary Leon Panetta called out Iran's hacking,
prompting fears of cyberwar.
The still-classified dam intrusion illustrates a top concern for
U.S. officials as they enter an age of digital state-on-state
conflict. America's power grid, factories, pipelines, bridges and
dams—all prime targets for digital armies—are sitting largely
unprotected on the Internet. And, unlike in a traditional war, it
is sometimes difficult to know whether or where an opponent has
struck. In the case of the dam hack, federal investigators
initially thought the target might have been a much larger dam in
Oregon.
Many of the computers controlling industrial systems are old and
predate the consumer Internet. In the early digital days, this was
touted as a security advantage. But companies, against the advice
of hacking gurus, increasingly brought them online in the past
decade as a way to add "smarts" to U.S. infrastructure. Often, they
are connected directly to office computer networks, which are
notoriously easy to breach.
These systems control the flow in pipelines, the movements of
drawbridges and water releases from dams. A hacker could
theoretically cause an explosion, a flood or a traffic jam.
The U.S. has more than 57,000 industrial-control systems
connected to the Internet, more than any other country, according
to researchers at Shodan, a search engine that catalogs each
machine online. They range from office air-conditioning units to
major pipelines and electrical-control systems.
Security experts say companies have done little to protect these
systems from would-be hackers.
"Everything is being integrated, which is great, but it's not
very secure," said Cesar Cerrudo, an Argentine researcher and chief
technology officer at IOActive Labs, a security-consulting firm. At
a hacker conference last year in Las Vegas, Mr. Cerrudo wowed the
audience when he showed how he could manipulate traffic lights in
major U.S. cities.
Operators of these systems "don't think about security," he
said.
The threat of physical damage is real. Last winter, the German
government said in a report that hackers broke into the control
system at a domestic steel plant and caused "massive" damage to a
blast furnace.
The U.S. and other governments use cyberweapons, too. In the
early years of President Barack Obama's term, the U.S. and Israel
used a sophisticated computer program to disable centrifuges at
Iran's nuclear facility at Natanz, according to former U.S.
officials. The virus unintentionally self-replicated and spread to
other networks, including systems at Chevron Corp. Executives at
the oil company said no damage occurred.
The Department of Homeland Security has publicly warned
industrial companies since 2011 to be more judicious in how they
connect these systems to the Internet. One 2014 missive said the
devices are poorly protected, "further increasing the chances of
both opportunistic and targeted" hacking attempts.
For the 12 months ended Sept. 30, the department had received
and responded to reports of 295 industrial-control-system hacking
incidents, up from 245 for fiscal year 2014, according to agency
statistics shared with The Wall Street Journal. The problem doesn't
appear to be getting better. In June, the department said a
"critical infrastructure asset owner" who suspected a breach hadn't
kept records of devices on its network, hindering the
investigation.
Most of the time, the hackers appear to be probing systems to
see how they are laid out and where they can get in, investigators
familiar with the incidents said.
The incident at the New York dam was a wake-up call for U.S.
officials, demonstrating that Iran had greater digital-warfare
capability than believed and could inflict real-world damage,
according to people familiar with the matter. At a congressional
hearing in February, Director of National Intelligence James
Clapper called Iranian hackers "motivated and unpredictable cyber
actors." Iranian officials didn't respond to a request for
comment.
The 2013 dam hack highlighted another challenge for America's
digital defenses: the fog of cyberwar. Amid a mix of three-letter
agencies, unclear Internet addresses and rules governing domestic
surveillance, U.S. officials at first weren't able to determine
where the hackers had infiltrated, three of the people familiar
with the incident said.
Hackers are believed to have gained access to the dam through a
cellular modem, according to an unclassified Homeland Security
summary of the case that doesn't specify the type of infrastructure
by name. Two people familiar with the incident said the summary
refers to the Bowman Avenue Dam, a small structure used for flood
control near Rye, N.Y.
Investigators said hackers didn't take control of the dam but
probed the system, according to people familiar with the
matter.
Homeland Security said it doesn't comment on specific incidents.
Spokesman S.Y. Lee said the department's "Industrial Control
Systems Cyber Emergency Response Team responds to cyber incidents,
vulnerabilities and threats" to critical infrastructure across the
U.S.
U.S. intelligence agencies noticed the intrusion as they
monitored computers they believed were linked to Iranian hackers
targeting American firms, according to people familiar with the
matter. U.S. officials had linked these hackers to repeated
disruptions at consumer-banking websites, including those of
Capital One Financial Corp., PNC Financial Services Group and
SunTrust Banks Inc., the Journal reported at the time.
Intelligence analysts then noticed that one of the machines was
crawling the Internet, looking for vulnerable U.S.
industrial-control systems. The hackers appeared to be focusing on
certain Internet addresses, according to the people.
Analysts at the National Security Agency relayed these addresses
to counterparts at Homeland Security, the people said.
Eventually, investigators linked one address to a "Bowman" dam.
But there are 31 dams in the U.S. that include the word "Bowman" in
their name, according to U.S. Army Corps of Engineers records.
Officials feared that hackers breached the systems at the Arthur
R. Bowman Dam in Oregon, a 245-foot-tall earthen structure that
irrigates local agriculture and prevents flooding in Prineville,
Ore., population: 9,200. The White House was notified of the
discovery, on the belief that it was a new escalation in the
ongoing digital conflict with Iran, three people familiar with the
incident said.
In response to a request for comment, the White House referred
The Wall Street Journal to Homeland Security.
Eventually, the trail led to the Bowman Avenue Dam, the people
said, near the village of Rye Brook, N.Y., a 20-foot-tall concrete
slab across Blind Brook, about 5 miles from Long Island Sound. It
was built in the mid-20th century for ice production, according to
municipal documents.
"It's very, very small," said Marcus Serrano, the manager of the
neighboring larger city of Rye. In 2013, Mr. Serrano said, several
FBI agents appeared at city offices and wanted to speak to the
city's information-technology manager about a hacking incident at
the dam. "There was very little discussion," Mr. Serrano said.
Chris Bradbury, administrator for the village of Rye Brook,
said, "I couldn't comment on that."
The FBI declined to comment.
Write to Danny Yadron at danny.yadron@wsj.com
(END) Dow Jones Newswires
December 21, 2015 07:35 ET (12:35 GMT)
Copyright (c) 2015 Dow Jones & Company, Inc.
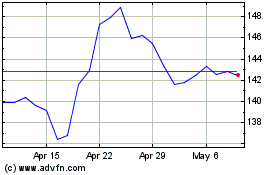
Capital One Financial (NYSE:COF)
Historical Stock Chart
From Mar 2024 to Apr 2024
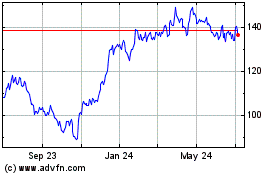
Capital One Financial (NYSE:COF)
Historical Stock Chart
From Apr 2023 to Apr 2024