Google Team Cracks Longtime Pillar of Internet Security
February 23 2017 - 1:05PM
Dow Jones News
By Robert McMillan
A cryptographic technology long central to internet security has
been dealt a knockout blow by researchers at Google and a Dutch
research institute.
In a paper published Thursday, the researchers demonstrate an
attack on an algorithm called SHA-1, which has been widely used
over the past 20 years to verify the authenticity of digital
documents.
SHA-1 has worked behind the scenes to guarantee that the
websites people visit are, in fact, what they claim to be. It is
what is known as a hash function -- a technique for turning any
digital document into a unique 40-digit sequence of letters and
numbers. That digital fingerprint serves as a quick way of
authenticating digital certificates, passwords, even office
documents.
Called a "collision attack," the researchers' technique is
something cryptographers have contemplated since 2005, when
researchers in China reported the first significant flaws in SHA-1.
Until now, "it was only a theoretical attack," said Marc Stevens, a
researcher with the Centrum Wiskunde & Informatica research
center in Amsterdam, which collaborated with Alphabet Inc.'s Google
unit on the effort. "We actually did it."
Once the most widely used algorithms of its type, SHA-1 is no
longer considered state of the art. It hasn't been used in the
production of digital certificates for websites since January 2016,
and is only "lightly used" by publicly available sites, according
to Ivan Ristic, founder of security vendor Qualys Inc.'s SSL Labs.
Browser makers are rolling out changes now that mark SHA-1 digital
certificates as untrustworthy.
But Mr. Stevens and Elie Bursztein, his collaborator at Google,
said the algorithm is still used often, particularly for validating
the integrity of documents. Mr. Ristic and other security experts
say, for example, that SHA-1 is likely to be found behind corporate
firewalls on devices where software upgrades are difficult, such as
point-of-sale terminals in retail stores.
In their attack, the researchers were able to create two
different documents that generated identical SHA-1 hash values,
essentially allowing hackers to swap out an authenticated digital
certificate for something else. It is the kind of swap that could
trick a computer into believing a malicious website was Google.com
or that a virus was legitimate software.
It was no easy feat. It took two years of painstaking
mathematical and software development work and close to 7,000 years
of chip processing time to crack the code, with CWI contributing
the mathematical expertise and a team of collaborators at Google
helping with the software and computing power.
The fact that this SHA-1 attack has moved from the realm of the
theoretical to the practical is a major development for
cryptographers because it is likely the most computationally
intensive cryptographic problem ever solved, said Dan Boneh, a
computer-science professor at Stanford University.
Security professionals need to take note too, he added.
"A lot of [chief security officers] in various organizations are
going to freak out and they're going to drop what they're doing and
they're going to buy new certificates," he said.
Now that they have solved the problem, Messrs. Stevens and
Bursztein said they believe that a subsequent attack would take
only about a month and cost about $100,000, using publicly
available cloud-computing servers. That would put it within range
of well-funded adversaries.
Google will wait 90 days before releasing the code behind its
attack and it has also developed a free system that will detect use
of this technique in files, the company said.
With its $100,000 computational price tag, the SHA-1 attack is
unlikely to be widely used, but such advanced techniques have
appeared in at least one previous attack. In 2012, Microsoft Corp.
disclosed that a collision attack was used to disguise malicious
software called Flame as a legitimate program on Windows systems.
Flame was eventually linked to a state-sponsored attack on several
Middle Eastern countries.
Write to Robert McMillan at robert.mcmillan@wsj.com
(END) Dow Jones Newswires
February 23, 2017 12:50 ET (17:50 GMT)
Copyright (c) 2017 Dow Jones & Company, Inc.
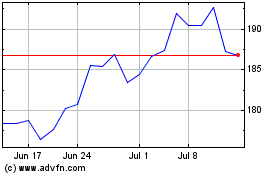
Alphabet (NASDAQ:GOOG)
Historical Stock Chart
From Aug 2024 to Sep 2024
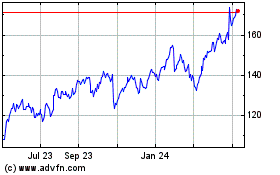
Alphabet (NASDAQ:GOOG)
Historical Stock Chart
From Sep 2023 to Sep 2024