Security Experts Say NSA-Linked Hacking Effort Was Itself Compromised
August 17 2016 - 4:31PM
Dow Jones News
By Robert McMillan
Evidence is mounting that a mysterious hacking group claiming to
have stolen data from a spying operation linked to the National
Security Agency is telling the truth.
Security vendor Kaspersky Labs ZAO, which first identified the
NSA-linked operation last year, said files released in the latest
hack use an unusual mathematical approach it had seen in that
operation's code. Kaspersky dubbed the operation the Equation
Group, and said it appeared to be supporting U.S. interests in
cyberspace.
The new files were released last weekend by a hacking group
calling itself the Shadow Brokers, which claims to have a bigger
cache of files it is offering to sell, They appear to be attack
code that targets security software on routers that direct computer
traffic around the internet.
"This code similarity makes us believe with a high degree of
confidence that the tools from the Shadow Brokers leak are related
to the malware from the Equation Group," Kaspersky said in a blog
post.
Two former NSA employees said the code published by the Shadow
Brokers looked authentic.
Security analysts, meanwhile, said several attacks that appear
in the files can in fact alter how internet routers handle certain
traffic.
None of the code appears to be of the high-value type that could
command the millions of dollars that the Shadow Brokers are
seeking, said Pedram Amini, chief technology officer of
computer-security firm InQuest LLC. He estimated the most
significant attacks, targeting products built by Cisco Systems
Inc., would fetch "tens of thousands of dollars" in the attack-code
market.
On Wednesday, Cisco confirmed that the Shadow Broker code took
advantage of a bug in its software that wasn't publicly known,
along with a second bug that it had patched in 2011. Fortinet Inc.,
another router maker identified in the attack code, confirmed that
the Shadow Broker code could be used to attack versions of its
products that were built in 2012 and earlier.
A third router maker, Juniper Networks Inc. didn't reply to
requests for comment.
The developments add to a murky and sometimes bewildering
affair. The previously unknown Shadow Brokers released an encrypted
version of files that it said contain hacking tools, pledging to
disclose the password that would unlock them for free to the world
if they raised 1 million bitcoins, or close to $600 million, in an
online auction.
Nicholas Weaver, a researcher with the International Computer
Science Institute who also has examined the files, said they appear
to be legitimate NSA attack code that was copied in mid-2013. Some
of the files dated months after former NSA contractor Edward
Snowden disclosed classified data that he had removed from the
NSA.
"Right now, I'd imagine that the folks at NSA are having rather
unpleasant conversations about what the other encrypted file might
contain," Mr. Weaver wrote in a blog post on Tuesday.
Mr. Weaver doesn't know who is behind the attacks. Like other
U.S. security experts, he said he believes that entities related to
the Russian government are likely suspects, amid allegations that
Russian hackers had compromised servers belonging to the Democratic
National Committee and other organizations.
Susan Hennessey, a Brookings Institution fellow and former
lawyer for the NSA, said a nation-state might be involved in the
Shadow Brokers breach and might be signaling the U.S. to be careful
about accusing foreign countries of cyberattacks. "It also has the
significance of potentially warning the United States that
attribution is also available against them," she said.
Kaspersky, which didn't explicitly link the Equation Group to
the NSA, declined to comment beyond its blog post. The NSA didn't
respond to requests for comment on the hacking group's claims, nor
did the Shadow Brokers respond to messages.
The Kaspersky analysis sheds some light on the situation, but
leaves many unanswered questions, including the identity of the
Shadow Brokers and what information the group actually has.
Former NSA employees interviewed by The Wall Street Journal said
it is extremely unlikely the attackers were able to access the full
catalog of NSA attack code. Some experts, including Mr. Snowden,
have said the Shadow Brokers may have accessed a "staging server"
that was used for a time by the Equation Group and wasn't properly
scrubbed of information.
"NSA malware staging servers getting hacked by a rival is not
new," Mr. Snowden said via Twitter on Tuesday. "A rival publicly
demonstrating they have done so is."
--Damian Paletta contributed to this article.
Write to Robert McMillan at Robert.Mcmillan@wsj.com
(END) Dow Jones Newswires
August 17, 2016 16:16 ET (20:16 GMT)
Copyright (c) 2016 Dow Jones & Company, Inc.
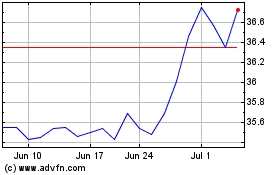
Juniper Networks (NYSE:JNPR)
Historical Stock Chart
From Mar 2024 to Apr 2024
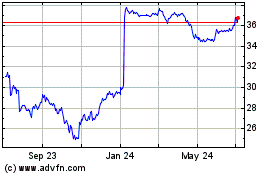
Juniper Networks (NYSE:JNPR)
Historical Stock Chart
From Apr 2023 to Apr 2024