Microsoft Says Russian Hackers Exploited Flaw in Windows
November 02 2016 - 4:20AM
Dow Jones News
The hackers believed responsible for breaking into computers at
the Democratic National Committee have exploited previously
undisclosed flaws in Microsoft Corp.'s Windows operating system and
Adobe Systems Inc.'s Flash software, Microsoft said Tuesday.
It is unclear if those hackers, reportedly tied to Russia, used
the newly disclosed vulnerabilities to hack into the DNC.
Microsoft Tuesday criticized Alphabet Inc's Google for publicly
identifying the Windows flaw on Monday, before Microsoft had had a
chance to issue a patch.
In a blog post, Terry Myerson, executive vice president of
Microsoft's Windows and Devices Group, said the hackers, whom the
company has dubbed Strontium, used "phishing" email messages
leveraging vulnerabilities in Windows and Adobe Flash to target a
specific set of customers.
People familiar with the matter said Strontium is the same group
that others have identified as Fancy Bear and accused of breaking
into the DNC's systems. U.S. government officials have blamed
Russia for hacks of the DNC and other prominent Washington players
this year.
Adobe said that it patched the flaw in its software on Oct. 26,
five days after being notified by Google of its existence. "We do
not have any information on the specific use of the exploit," a
spokeswoman said by email.
An Alphabet spokesman declined to comment.
Microsoft expects to issue a patch to resolve the issue Nov. 8.
A company spokesman declined to comment beyond the blog post.
In the blog post, Mr. Myerson said users of its Edge browser on
computers running the most current version of its Windows 10
operating system are protected from the attack.
In a security report last year, Microsoft said Strontium has
been active since 2007 and is primarily interested in "sensitive
information" rather than financial gain. According to the report,
Strontium's targets have included governments, diplomatic
institutions, military forces and installations in NATO member
states, as well as journalists and political advisers.
"The group's persistent use of spear phishing tactics and access
to previously undiscovered zero-day exploits have made it a highly
resilient threat," the report said.
In phishing attacks, hackers trick victims into visiting
webpages that they control, either to trick the victim into
disclosing a username and password, or to use specially crafted
software to take control of the victim's computer. A "zero-day"
exploit is an attack that leverages a previously undisclosed
software bug.
In its security report, Microsoft noted that Strontium typically
identifies and profiles potential victims using email lists and
information harvested from public forums or social-networking
sites. The group relies on past phishing attacks to augment its
data, sifting through emails it's collected to identify connections
between prior targets and the current target.
The group that security investigators have linked to breaches at
the Democratic National Committee and the Democratic Congressional
Campaign Committee has been given several names by computer
security firms. CrowdStrike Inc. calls it "Fancy Bear." Microsoft
uses the name Strontium.
Files taken from the DNC and others have been posted to the
internet by WikiLeaks and another group calling itself DC
Leaks.
Last month, U.S. intelligence agencies took the unusual step of
jointly accusing the Russian government of attempted interference
in the U.S. election by leaking email messages that it had hacked
from the Democratic National Committee and others. Russia has
denied involvement in these hacks.
Write to Jay Greene at Jay.Greene@wsj.com and Robert McMillan at
Robert.Mcmillan@wsj.com
(END) Dow Jones Newswires
November 02, 2016 04:05 ET (08:05 GMT)
Copyright (c) 2016 Dow Jones & Company, Inc.
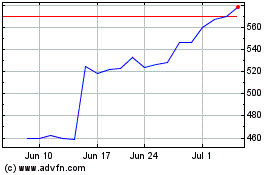
Adobe (NASDAQ:ADBE)
Historical Stock Chart
From Mar 2024 to Apr 2024
Adobe (NASDAQ:ADBE)
Historical Stock Chart
From Apr 2023 to Apr 2024
