By Robert McMillan
Just after 8 a.m. on Tuesday morning, mobile phones belonging to
executives on Apple Inc.'s security team began to ring. WikiLeaks
had just published a massive trove of documents, purportedly taken
from the Central Intelligence Agency, that described the spy
agency's intrusion capabilities for computers and other gadgets,
including iPhones.
Apple engineers quickly began calling colleagues to bring them
up to speed on the data dump and to coordinate the company's
response to this new security threat, according to a person
familiar with the situation.
Companies across the technology industry have rushed to assess
the damage from the 8,761 documents released by WikiLeaks. The
documents, which WikiLeaks said reveal the scope of the CIA's
covert hacking program, showed that the agency was exploiting bugs
in mobile phones, routers and even internet-connected television
sets in support of its spying activities.
A CIA spokesman wouldn't confirm whether the leaked documents
were authentic or comment on the status of any investigation into
the leak, but he criticized WikiLeaks' actions.
For companies such as Apple, Alphabet Inc.'s Google, Samsung
Electronics Co. and Microsoft Corp., the risks are substantial. The
CIA's tools apparently can be used to gain unauthorized access to
computers and smartphones. And because of the high-profile nature
of the leak, the tools are likely to be widely used once they are
disclosed. WikiLeaks hasn't disclosed the actual code the CIA used
in its operations, though the group says that the code "appears to
have been circulated among former U.S. government hackers and
contractors in an unauthorized manner, " and security experts say
it is likely to be made public in the near future.
"It's a very, very busy few weeks that has been triggered by
this," said Alex Rice, chief technology officer with HackerOne
Inc., a San Francisco company that helps corporations develop
bug-finding programs. "It's not panic; it's not chaos; but it's a
lot more midnight oil being burned than usual."
It is difficult to precisely identify all bugs from the
WikiLeaks documents that have been released so far, but they
contain enough bread crumbs for some companies to identify some
flaws in their products. On Wednesday, Apple, Microsoft, Samsung,
and Google all said that they were still investigating, but Apple
and Google expressed confidence that the impact might be limited
thanks to measures already taken to enhance its iOS mobile
operating system.
"While our initial analysis indicates that many of the issues
leaked today were already patched in the latest iOS, we will
continue work to rapidly address any identified vulnerabilities,"
an Apple spokesman said.
In a statement Wednesday Google said, "As we've reviewed the
documents, we're confident that security updates and protections in
both Chrome and Android already shield users from many of these
alleged vulnerabilities. Our analysis is ongoing."
Companies now find themselves in a difficult position: They
believe that at least two organizations have access to hacking code
that exploits their products -- the CIA and WikiLeaks -- but
neither one is sharing this software.
Cisco Systems Inc., which makes routers and other internet
equipment, said that without more information on the exact tools
and malware involved, "the scope of action that can be taken by
Cisco is limited." In a blog post, it said its preliminary analysis
shows malware targeting its devices could enable activities
including data collection and redirecting of internet traffic, and
that the tools appeared designed to evade detection on routers and
switches. Cisco said it expects WikiLeaks will release the
malware.
Big tech companies including Apple and Google regularly speak
with U.S. intelligence agencies and have designated people
internally with federal security clearance that allows the
companies to handle sensitive requests and information, said a
person who has worked with the companies on security matters.
But the CIA is unlikely to provide information on its attacks,
because that data could be used to determine whom it has targeted
for surveillance, said Dan Guido, director at hack/secure, a
cybersecurity investment firm. "They wouldn't do this," he
said.
A CIA spokesman declined to comment on whether the agency would
work with technology companies to fix these flaws.
WikiLeaks on Wednesday ran an online poll asking its users if it
should work directly with technology companies to help quickly fix
the vulnerabilities used by the CIA. As of Wednesday afternoon, 53%
of the 8,500 respondents had voted yes. WikiLeaks didn't return
messages seeking comment.
Over the past decade, the federal government set up a program
called the Vulnerability Equities Process to share information on
security flaws it discovers with U.S. companies. Officials are
discussing whether to use that process to disclose more information
about the issues described in the documents released by WikiLeaks,
but that is likely to involve a lengthy interagency review, said
one person familiar with the situation.
The White House, which manages the process, didn't immediately
respond to an email message seeking comment.
Meanwhile, the WikiLeaks release is likely to cast a spotlight
on the Vulnerability Equities Process and the question of whether
or not the government should do more to improve the security of
technology products and whether the CIA should have disclosed some
of these bugs previously. "It would seem strange that during a
period of almost a decade that none of these vulnerabilities fit
the criteria for disclosure under the Vulnerability Equities
Process," said HackerOne's Mr. Rice.
Even when this week's fire drill is done, it's a scenario that
could very well repeat itself again if WikiLeaks discloses new
secrets allegedly taken from the CIA. The group says that it has
now disclosed just 1% of the documents in its possession. "If it is
the case that they have so much more, that, I think, will have a
lot of people quite nervous," said Thomas Rid, a professor of
security studies with King's College London.
--Tripp Mickle contributed to this article.
Write to Robert McMillan at Robert.Mcmillan@wsj.com
(END) Dow Jones Newswires
March 08, 2017 22:08 ET (03:08 GMT)
Copyright (c) 2017 Dow Jones & Company, Inc.
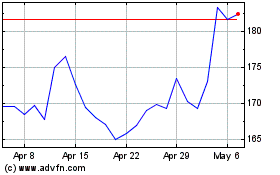
Apple (NASDAQ:AAPL)
Historical Stock Chart
From Mar 2024 to Apr 2024
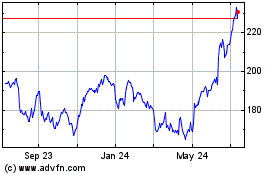
Apple (NASDAQ:AAPL)
Historical Stock Chart
From Apr 2023 to Apr 2024